Overview
1️⃣ General Flow Webhooks
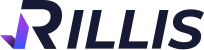
You can configure these webhooks when creating or editing a flow by clicking the "<>" button (with the tooltip "Integrate SDK") as shown in the following image:
2️⃣ Step-by-Step Webhooks
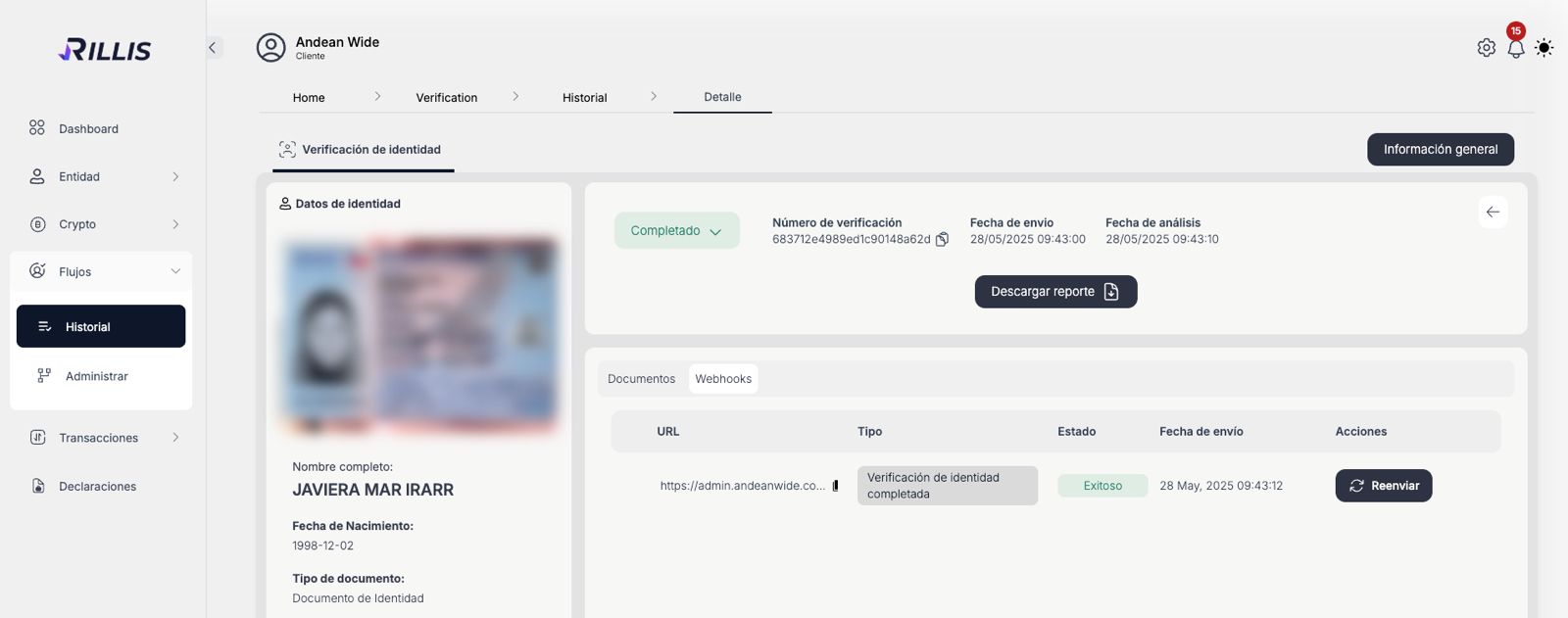
These can be configured by navigating to the "Webhook" tab within each flow. This way, you can capture events as they occur in real-time.
Summary Table of Flow API Webhooks
| Webhook Type | Description | Step |
|---|---|---|
FLOW_COMPLETED | Triggered when a flow and all related services are fully completed. | Flow completion |
FLOW_REJECTED | Triggered when a flow is rejected (e.g., final decision of no approval). | Flow completion |
VERIFICATION_IDENTITY_REJECTED | Triggered when an identity verification is rejected. | Identity Verification |
VERIFICATION_IDENTITY_COMPLETED | Triggered when an identity verification is approved. | Identity Verification |
VERIFICATION_IDENTITY_UPDATED | Triggered when an identity verification is manually updated. | Identity Verification |
ONBOARDING_FORM_INDIVIDUAL_COMPLETED | Triggered when an individual form is completed (pending review). | Onboarding Individual |
ONBOARDING_FORM_INDIVIDUAL_REJECTED | Triggered when an individual onboarding form is rejected. | Onboarding Individual |
ONBOARDING_FORM_COMPANY_COMPLETED | Triggered when a company form is completed (pending or approved). | Onboarding Company |
ONBOARDING_FORM_COMPANY_REJECTED | Triggered when a company onboarding form is rejected. | Onboarding Company |
How Webhooks Work
POST request to your configured webhook URL containing the event data in JSON format. The payload typically includes:FLOW_COMPLETED).Your webhook endpoint must respond with a 200 HTTP status code to confirm receipt. If Rillis does not receive this response, it will automatically retry the notification several times.
🔐 Securing Your Webhooks (Signature Validation)
x-signature: The HMAC-SHA256 signature of the payload.x-timestamp: The Unix timestamp (in seconds) when the signature was generated.How to Validate the Signature (Step-by-Step)
Step 1: Extract Headers and Payload
x-signature and x-timestamp from the request headers, and capture the raw JSON body.Step 2: Sort the Payload Recursively
Step 3: Recreate the Signature
Step 4: Compare Signatures Safely
Security Best Practices
1.
webhook_key: Ensure it is never visible in client-side code, server logs, or error responses.2.
webhook_key securely on your server using environment variables (e.g., .env files).3.
x-timestamp header against your server's current time to prevent replay attacks (a 5-minute window is recommended).4.
timingSafeEqual (or your programming language's equivalent) when comparing signatures to prevent timing attacks.5.
Modified at 2026-02-23 17:57:18